The Essential Guide to Cyber Security Software for Startups: Protecting Your Growth in 2026
For the modern startup, speed is the ultimate currency. You iterate fast, hire quickly, and scale aggressively. However, in this race toward market dominance, security is often treated as a “tomorrow problem.” In 2026, this mindset is no longer just risky; it is potentially fatal. With the average cost of a data breach for small businesses now reaching record highs, cyber security software for startups has transitioned from a luxury line item to a foundational requirement.
Cybercriminals increasingly target early-stage companies, viewing them as high-value, low-defense entry points into larger supply chains. As a business owner or decision-maker, your challenge is to build a robust defense without stifling the agility that makes your company thrive. This guide provides a strategic roadmap for selecting the right security tools, ensuring your intellectual property, customer data, and brand reputation remain shielded as you scale. In the digital economy of 2026, security is not a barrier to growth—it is the catalyst that makes sustainable growth possible.
—
Why Startups Are High-Value Targets for Cybercriminals
There is a persistent myth in the founder community that startups are “too small to be noticed” by hackers. The reality in 2026 is quite the opposite. Startups are often targeted precisely because they possess high-value intellectual property (IP) and sensitive customer data but lack the sophisticated security infrastructure of a Fortune 500 company.
Cybercriminals use automated scripts to scan for vulnerabilities across the internet, making no distinction between a three-person garage team and a global corporation. Furthermore, startups often act as “soft targets” for supply chain attacks. If your software integrates with larger enterprises, a breach in your system could provide a backdoor for hackers to infiltrate your much larger clients.
Beyond the immediate threat of data theft, the regulatory landscape has tightened significantly. Between evolving global data privacy laws and the strict requirements of SOC2 or ISO 27001 compliance, a single security lapse can result in crippling fines or the loss of vital enterprise contracts. For a startup, a breach isn’t just an IT issue; it’s a trust issue that can lead to immediate churn and investor withdrawal.
Core Components of a Startup Security Stack
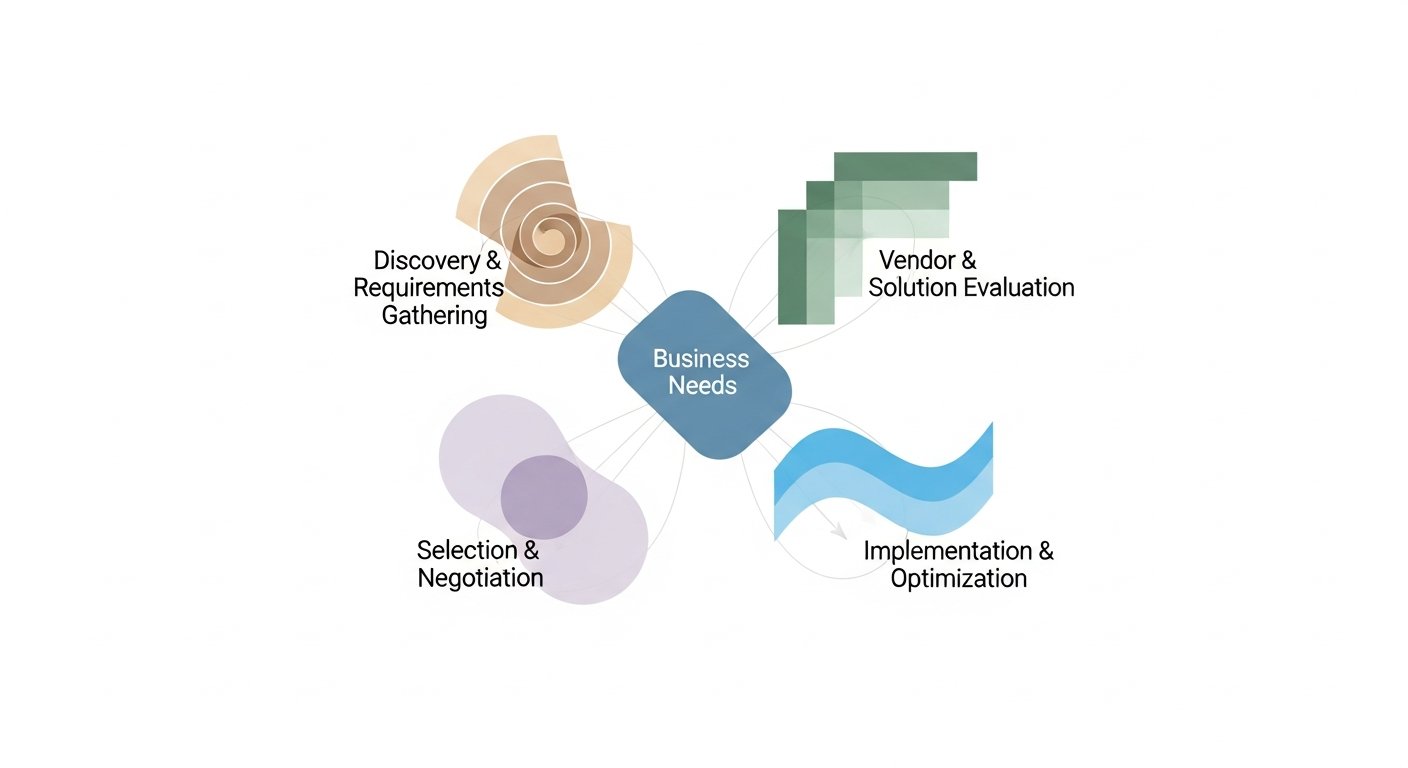
Building a security stack doesn’t mean buying every tool on the market. For a startup, the goal is to cover the most common attack vectors with integrated, high-ROI solutions. In 2026, a lean but effective security stack should focus on four primary pillars:
#
1. Identity and Access Management (IAM)
Identity is the new perimeter. As remote and hybrid work models remain the standard, your employees are accessing company data from various locations and devices. IAM software ensures that the right people have access to the right resources. Look for tools that offer Single Sign-On (SSO) and Multi-Factor Authentication (MFA). In 2026, “passwordless” authentication has become a preferred standard to eliminate the risks associated with compromised credentials.
#
2. Endpoint Detection and Response (EDR)
The days of simple antivirus software are over. EDR tools provide real-time monitoring and response for all company devices (laptops, mobiles, servers). These tools use AI to detect behavioral anomalies—such as a laptop suddenly trying to export a massive database—and can automatically quarantine the device before the threat spreads.
#
3. Cloud Security Posture Management (CSPM)
Since most startups are born in the cloud (AWS, Azure, Google Cloud), misconfigurations are a leading cause of data leaks. CSPM software continuously scans your cloud environment to ensure that storage buckets aren’t left open to the public and that your infrastructure adheres to security best practices.
#
4. Email Security and Anti-Phishing
Phishing remains the most common entry point for ransomware. Modern email security software for startups uses natural language processing (NLP) to detect sophisticated “business email compromise” (BEC) attempts that traditional filters might miss.
Evaluating Cyber Security Software: A Checklist for Founders
When choosing software, founders often fall into the trap of buying “too much tool” for their current stage or, conversely, selecting a tool that they will outgrow in six months. Here is a checklist to use during your evaluation process:
* **Automation-First Design:** As a startup, you likely don’t have a 24/7 Security Operations Center (SOC). Your software must be able to automate the “detect and remediate” cycle without constant human intervention.
* **Ease of Deployment:** If a tool requires three months of professional services to set up, it’s not for you. Look for “SaaS-native” tools that offer one-click integrations with your existing stack (Slack, GitHub, G-Suite).
* **Scalability:** Does the pricing model scale with you? Avoid vendors that lock you into massive multi-year contracts with high seat minimums. You want a partner that grows as you grow.
* **Visibility and Reporting:** Can the software provide a “single pane of glass” view? You need a dashboard that tells you your security health at a glance, which is also invaluable when showing “due diligence” to potential investors or auditors.
* **API-Centricity:** In 2026, the best security tools are those that play well with others. Ensure the software has a robust API so your engineering team can integrate security alerts into their existing workflows.
Top Categories of Cyber Security Software for Startups in 2026
To help you categorize your spending, let’s look at the specific types of software that offer the highest protection-to-cost ratio for emerging companies.
#
Vulnerability Management
These tools act like a “digital home inspection.” They scan your code, your website, and your network for known weaknesses. For startups, “Shift Left” security—where you scan code for vulnerabilities *before* it’s even deployed—is a game-changer. It’s significantly cheaper to fix a bug in the development phase than it is to patch a live exploit.
#
Compliance Automation
Achieving SOC2 or HIPAA compliance used to take a year and cost six figures. In 2026, compliance automation software connects to your entire tech stack and automatically gathers evidence of your security controls. This allows startups to “get enterprise-ready” in weeks rather than months, opening doors to larger sales cycles.
#
Managed Detection and Response (MDR)
For startups that have moved past the seed stage but aren’t ready for a full internal security team, MDR is the middle ground. It is essentially “Security-as-a-Service,” where you buy the software, but it is monitored by a third-party team of experts who jump in if a serious threat is detected.
#
Data Loss Prevention (DLP)
DLP software monitors the movement of sensitive data. If an employee tries to upload your proprietary source code to a personal cloud storage account or email a customer list to a competitor, the software blocks the action and alerts management.
Balancing Budget and Protection: The “Shift Left” Philosophy
One of the biggest hurdles for startups is the perceived cost of security. However, in 2026, the most successful companies are adopting a “Shift Left” philosophy. This means integrating security at the very beginning of the software development life cycle (SDLC) rather than “bolting it on” at the end.
When you incorporate security software into your developers’ IDEs (Integrated Development Environments), you prevent vulnerabilities from ever reaching production. This reduces the need for expensive “clean-up” operations later. Furthermore, many enterprise-grade security vendors now offer “Startup Programs.” These programs provide deep discounts (sometimes up to 90% off) for the first year to companies that meet certain funding or age criteria.
Don’t be afraid to leverage these programs. They allow you to build on a world-class foundation for the price of a mid-tier SaaS subscription. By investing in the right cyber security software for startups early, you aren’t just spending money; you are reducing your future “security debt.”
How to Implement Security Software Without Slowing Down Innovation
A common complaint from engineering teams is that security tools “get in the way” of shipping code. To maintain your startup’s velocity, implementation must be strategic.
First, **prioritize friction-less tools.** If a tool requires a developer to change their entire workflow, it will be ignored or bypassed. Choose tools that meet developers where they are—for example, security alerts that appear directly in GitHub pull requests or Slack channels.
Second, **adopt a phased approach.** Do not try to implement MFA, EDR, CSPM, and DLP all in the same week. Start with the “low-hanging fruit” like Identity Management and Email Security. Once those are bedded in and the team is comfortable, move on to more complex infrastructure monitoring.
Third, **foster a security-first culture.** Software is only as effective as the people using it. Use your security tools to educate, not just to police. Many modern tools offer “just-in-time” training; for example, if a user clicks a simulated phishing link, the software immediately presents a 30-second video explaining what they missed. This turns a potential weakness into a learning moment, reinforcing your security posture without creating a culture of fear.
—
FAQ: Cyber Security Software for Startups
#
1. What is the very first security tool a startup should buy?
The most critical first step is Identity and Access Management (IAM), specifically a tool that manages Single Sign-On (SSO) and Multi-Factor Authentication (MFA). Since compromised credentials are the leading cause of breaches, securing “the keys to the kingdom” should be your top priority before moving on to more specialized tools.
#
2. Can we rely on free or open-source security tools?
Yes, but with caveats. Open-source tools can be excellent for vulnerability scanning or firewalls, but they often require significant manual configuration and expertise to maintain. For a lean startup, the time spent managing a “free” tool often costs more in developer hours than paying for a user-friendly SaaS solution that offers automation and support.
#
3. How much of our budget should be allocated to cyber security?
While it varies by industry, a general rule for startups in 2026 is to allocate 5% to 10% of the total IT budget to security. If you are in a highly regulated field like Fintech or Medtech, this percentage may need to be higher to cover specific compliance and data protection requirements.
#
4. Do we need cyber security software if we are 100% on the cloud?
Absolutely. While cloud providers like AWS or Google manage the security *of* the cloud (the physical servers), you are responsible for security *in* the cloud (your data, configurations, and user access). Misconfigured cloud settings are one of the most common ways startups lose data.
#
5. Will having security software lower my cyber insurance premiums?
Yes. In 2026, most cyber insurance providers require proof of specific protections—like MFA and EDR—before they will even issue a policy. Implementing robust security software not only makes you more insurable but can significantly lower your annual premiums by demonstrating a lower risk profile.
—
Conclusion: Security as a Competitive Advantage
In the competitive landscape of 2026, cyber security software for startups is no longer a defensive necessity—it is a competitive advantage. When you can demonstrate to your customers, partners, and investors that their data is protected by a sophisticated, automated security stack, you build a level of trust that your less-prepared competitors cannot match.
Protecting your startup doesn’t require a multi-million dollar budget or a team of fifty security engineers. It requires a strategic selection of tools that offer maximum visibility, automated protection, and seamless integration. By focusing on identity, protecting your endpoints, and automating your compliance, you create a resilient foundation. This allows your team to focus on what they do best: innovating, disrupting, and growing your business with the peace of mind that your digital assets are secure. The best time to secure your startup was the day you founded it; the second best time is today.